[ad_1]
April 25, 2022
Analysis By: Alexey Bukhteyev
Highlights
- Verify Level Analysis (CPR) found a vulnerability within the net model of Ever Surf pockets, a part of the Everscale blockchain ecosystem
- By exploiting the vulnerability, an attacker may have gained full management over sufferer’s pockets
- After accountable disclosure, CPR collaborated with the Everscale groups, which acknowledged the vulnerability and launched a brand new desktop model to interchange the susceptible net model
Background
Blockchain expertise and decentralized purposes (dAPPs) present customers with an a variety of benefits. For instance, customers can make the most of the service with out creating an account and it may be carried out as a single-page software written in JavaScript. This kind of software doesn’t require communication with a centralized infrastructure, reminiscent of an internet server, and it may well work together with the blockchain immediately or through the use of a browser extension like Metamask.
On this case, the person is recognized utilizing keys which are saved solely on an area machine inside a browser extension or an internet pockets. If a decentralized software or a pockets shops delicate information regionally, it should guarantee this information is reliably protected. Normally, dAPPs run contained in the browser and subsequently could also be susceptible to assaults reminiscent of XSS.
This analysis describes the vulnerability discovered within the net model of Ever Surf, a pockets for the Everscale blockchain (previously Free TON). By exploiting the vulnerability, it’s doable to decrypt the non-public keys and seed phrases which are saved within the browser’s native storage. In different phrases, attackers may acquire full management over sufferer’s wallets.
Accountable disclosure and collaboration with Everscale
CPR disclosed the vulnerability to Ever Surf builders who then launched a desktop model that mitigates this vulnerability. The net model is now declared deprecated and will solely be used for improvement functions. Seed phrases from accounts that retailer actual worth in crypto shouldn’t be used within the net model of Ever Surf.
Vulnerability description
Ever Surf is a cross-platform messenger, a blockchain browser, and a crypto pockets for Everscale blockchain. It’s written in React Native and is offered in Google Play Market and Apple Retailer. There’s additionally a web version of Ever Surf that runs on any platform.
Determine 1 – Net model of Ever Surf
Surf doesn’t require a backend to work with the blockchain as a result of it implements a non-custodial pockets. This implies the keys required to signal transactions are solely saved on the person’s system. Operations with the blockchain are carried out completely on the shopper’s aspect. Subsequently, like different non-custodial wallets, it doesn’t have a registration utilizing login names and passwords.
When customers run the appliance for the primary time, it suggests creating a brand new pockets. Surf generates a seed phrase and a pair of the general public and the non-public keys. As well as, the person is prompted to create a 6-digit PIN code:
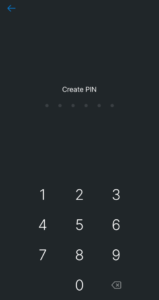
Determine 2 – PIN code setup in Ever Surf
This PIN is then used to log into the appliance and in addition to verify transactions. Surf has a safety towards brute-forcing the PIN code. When customers enter an incorrect PIN code 5 instances in a row, the appliance is momentary blocked and customers are prevented from getting into further PIN codes:
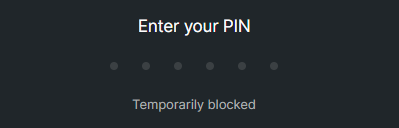
Determine 3 – Ever Surf prevents brute-forcing PIN codes
Even with out such safety, the efficiency of manually brute-forcing PIN codes can’t be environment friendly sufficient to hassle with usually. Subsequently, to implement an actual assault, attackers would want to extract the keystore from the appliance.
The created keys and the seed phrase are saved within the net browser’s local storage. The native storage is a key-value storage accessed from JavaScript utilizing the “localStorage” property. For instance:
// Retailer worth on the browser past the period of the session
localStorage.setItem('key', 'worth');
// Retrieve worth (persists even after closing and re-opening the browser)
alert(localStorage.getItem('key'));
Surf shops the keys and the seed phrase within the “surf.ton.pockets” key of the native storage within the following format:
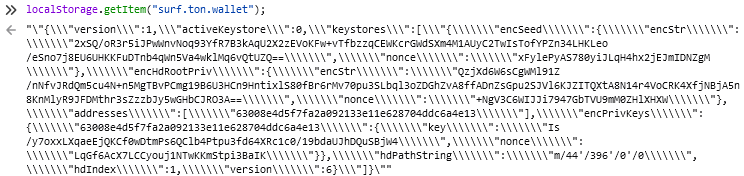
Determine 4 – Encrypted pockets information is saved within the browser’s localStorage
Native storage is just not protected in net browsers. For instance, in Firefox it’s saved in a non-encrypted SQLite database within the file:
MozillaFirefoxProfiles{profile_name}webappstore.sqlite
Chrome shops the native storage within the non-encrypted kind in a LevelDB database within the folder:
GoogleChromeUser DataDefaultLocal Storageleveldb
Which means that a human with bodily entry to the pc or any software or malware reminiscent of an infostealer can get hold of this information.
As well as, localStorage could be accessed by a browser extension, which may then leak the saved information. To display this, we created a easy Chrome net extension with the next code:
alert(localStorage.getItem("surf.ton.pockets"));
If we open the Surf web site after putting in the extension, we see the message containing the encrypted keystore:
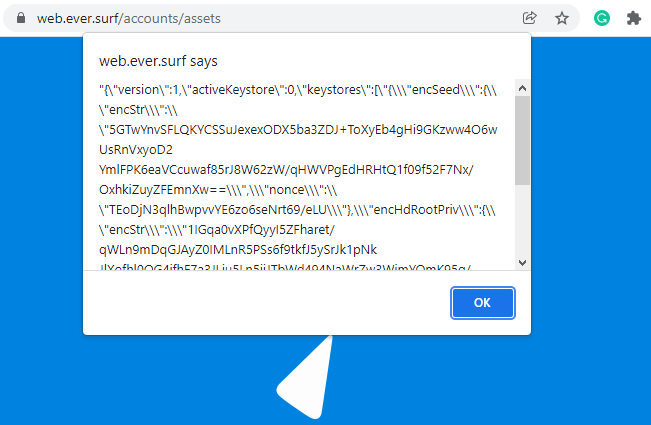
Determine 5 – Extracting encrypted pockets information from localStorage utilizing a browser extension
Subsequently, the browser’s native storage can’t be thought-about safe sufficient.
The accountability for the reliability of the saved information encryption rests completely with the online software.
Web sites that require registration, reminiscent of well-known social networks, could not rely solely on the information saved in cookies or native storage. They might additionally verify the online browser and the person’s IP tackle, and require further person verification in case of suspicious actions. That is unattainable with Surf as a result of the information required to manage a person’s pockets is saved completely on their laptop. The one safety for his or her funds is robust encryption.
Keystore encryption
Sadly, Surf is just not open-source. Subsequently, Verify Level researchers needed to analyze the minified JavaScript software bundle to grasp the logic.
Though an attacker could be primarily within the keys decryption, it is sufficient to get the seed phrase which can be utilized to revive the keys. The applying decrypts the seed phrase and reveals it to the person after getting into the PIN code:
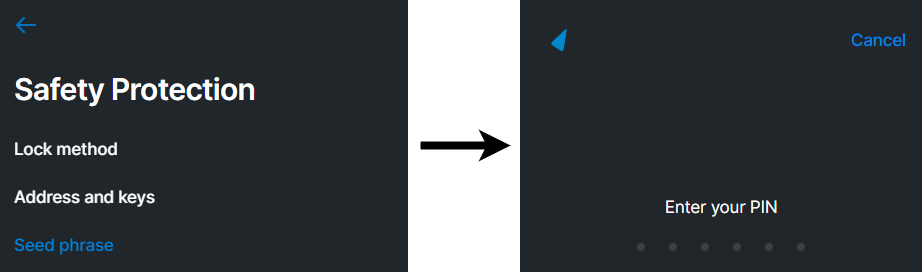
Determine 6 – Surf asks for the PIN code earlier than displaying the seed phrase
Subsequently, to seek out the place the decryption happens, CPR first anchored to the perform that fetches the seed phrase. On this perform, the askForPassword perform is named and receives the encrypted keystore.
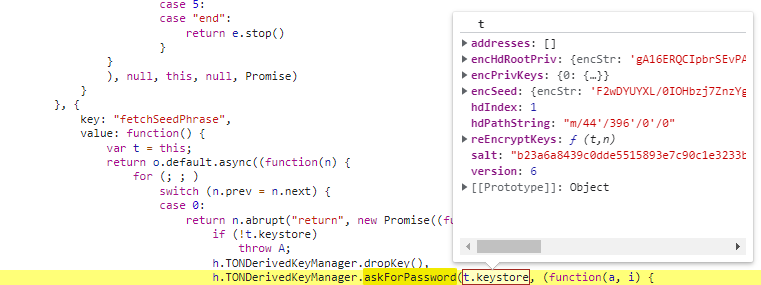
Determine 7 – The perform answerable for fetching the seed phrase asks for the PIN code
The askForPassword perform performs the PIN code validation by calling the validatePassword perform.
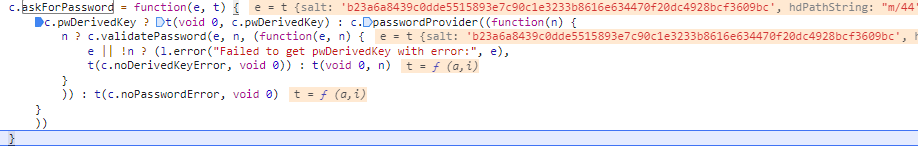
Determine 8 – The askForPassword perform reads and validates the PIN code
Crucial actions are carried out all through the PIN code validation. By calling the deriveKeyFromPasswordAndSalt perform, Surf generates the derived key, which is used to decrypt the keystore. Then, within the isDerivedKeyCorrect perform, Surf performs the decryption utilizing nacl_secret_box_open:
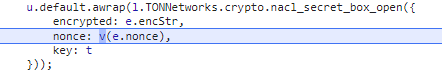
Determine 9 – Surf decrypts the keys utilizing nacl_secret_box_open.
These are the arguments for nacl_secret_box_open:
- encrypted – Encrypted string in base64-encoded kind
- nonce – Hex-encoded nonce
- key – 64 symbols hex-encoded key derived from the PIN-code
The values “encrypted” and “nonce” are taken from the keystore (encStr and nonce):
{"encSeed": {
"encStr":"6rjkbh88WXkrJWl4os3cjRzvZkQGlnV39U3YvLYUrM7yzf6h79XxXX/VziNde2bkPeSnJZ11Yi4T8CFgPJMyI1W+EN0Yzw+FDdtTq5gaKHjk5nF60CSHZ4qKXObIQ7zBbped",
"nonce":"2Tdr9FFP0RcpjecwcS8XtcC5M2/FRY+I"
}}
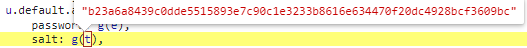
The subsequent step is to grasp how the derived key seems. Contained in the deriveKeyFromPasswordAndSalt, Surf derives the decryption key from the PIN code utilizing the Scrypt key derivation function with the next arguments:
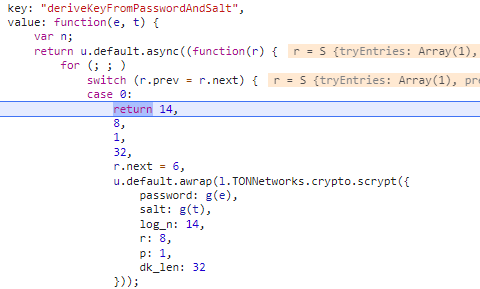
Determine 10 – Surf derives the keystore decryption key from the entered PIN code and salt utilizing Scrypt
These are the arguments for scrypt:
- password – Base64-encoded PIN-code
- salt – Salt worth within the base64-encoded kind
Because the password is entered by the person, the one lacking piece is the salt worth. The salt worth is calculated on the shopper’s system and has two roles:
- It isn’t saved within the keystore. This could imply decryption is unattainable if the encrypted keys had been leaked and the attacker doesn’t know learn how to calculate the salt.
- Protects the ensuing worth towards rainbow table assaults.
Salt is calculated as SHA256 hash of one of many values returned by the DeviceInfo.getUniqueId perform of the react-native-device-info bundle:
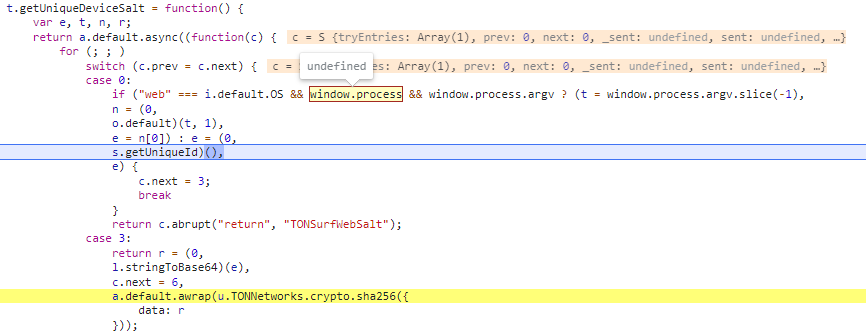
Determine 11 – Surf generates the salt by hashing the worth returned by DeviceInfo.getUniqueId()
However, there’s an alternative choice. The salt could be calculated as SHA256 of the window.course of.argv.slice(-1) worth. In an internet browser, the window.course of is undefined. Subsequently, DeviceInfo.getUniqueId is at all times used.
After checking react-native-device-info documentation, researchers see that it isn’t supported in an internet browser:
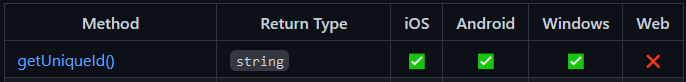
Determine 12 – getUniqueId() is just not supported in an internet browser
In an internet browser, this perform at all times returns the worth “unknown”:
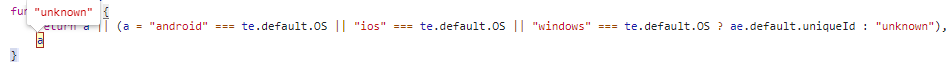
Subsequently, the salt is at all times the identical and could be simply calculated as sha256(“unknown”) and is the same as “b23a6a8439c0dde5515893e7c90c1e3233b8616e634470f20dc4928bcf3609bc”:
Determine 13 – The salt is at all times equal to sha256(“unknown”)
Assault
CPR roughly re-implemented the important thing derivation and keystore decryption in NodeJS and carried out a brute-force assault on the PIN code.
This resulted in a efficiency of 95 passwords per second on 4-core Intel Core i7 CPU. Though this isn’t a really excessive velocity, it’s adequate for the assault on a 6-digit PIN code. Within the worst case state of affairs, checking 10^6 doable variants means your entire assault takes roughly 175 minutes.
For our experiment, we created a brand new key in Surf and dumped the keystore from the browser’s native storage:
{
"encSeed": {
"encStr":"6rjkbh88WXkrJWl4os3cjRzvZkQGlnV39U3YvLYUrM7yzf6h79XxXX/VziNde2bkPeSnJZ11Yi4T8CFgPJMyI1W+EN0Yzw+FDdtTq5gaKHjk5nF60CSHZ4qKXObIQ7zBbped",
"nonce":"2Tdr9FFP0RcpjecwcS8XtcC5M2/FRY+I"
}
}
In our case, the assault took 38 minutes. On the finish, we obtained the derived key and decrypted the seed phrase that can be utilized to revive the keys on one other system:
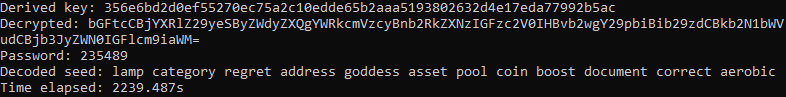
Determine 14 – PIN code brute power outcomes
If cybercriminals carry out scalable assaults utilizing infostealers, they might gather enormous numbers of encrypted keys and seed phrases. In the event that they attempt to decrypt them one after the other, it could take a considerably very long time.
Nevertheless, for the reason that salt for all encrypted information from completely different customers is similar, the important thing derivation perform Scrypt could be known as solely as soon as per checked PIN code. Whereas the Scrypt perform is computationally intensive, the nacl_secret_box_open perform that’s used for the decryption could be very quick. This permits brute-forcing the PIN codes for a number of wallets with no vital efficiency impression.
In comparison with brute-forcing PIN codes for one encrypted seed phrase when the efficiency was 95 PIN codes per second, once we tried to power the PIN code for 100 encrypted seed phrases concurrently, we obtained a efficiency of 79 passwords per second.
Tricks to keep protected
We wish to remind you that blockchain transactions are irreversible. In blockchain, not like a financial institution, you can not block a stolen card or dispute a transaction. If the keys on your pockets are stolen, your crypto funds can develop into straightforward prey for cybercriminals, and nobody might help to return your a refund. To stop theft of the keys, we advocate:
- Don’t observe suspicious hyperlinks particularly in the event that they acquired from strangers.
- Hold your OS and anti-virus software program up to date.
- Don’t obtain software program and browser extensions from unverified sources.
Conclusion
Because the browser’s native storage is unprotected, the information saved there have to be securely encrypted. Even supposing Surf makes use of dependable cryptographic libraries for the important thing derivation and the encryption, the delicate information within the net model of Surf doesn’t seem to have sufficient safety.
CPR’s PoC reveals that the mixture of the problems discovered presents a number of assault vectors that may result in an attacker acquiring non-public keys and seed phrases in clear textual content, which may then be used to achieve full management over the sufferer’s pockets.
Verify Level Researchers collaborated with the Ever Surf groups which determined that the susceptible net model might be deprecated and changed with a desktop model. Ever Surf revealed an article concerning the new model through which they said:
“Verify Level Analysis performed their very own impartial analysis concerning the safety standing of the Surf net model and came upon its weak point. We adopted this report, checked all the pieces and ensured that the vulnerability exists. Our net model can not present a safe use of password-based KDF due to an incapacity to supply a singular salt reminiscent of system ID for that platform. In easy phrases, which means there’s a theoretical solution to get entry to your pockets and belongings on it.
Subsequently, we wanted to take fast steps to eradicate it in order to not put our customers in danger. It grew to become clear that we can not longer postpone the discharge of the Surf desktop app. Our fundamental concept was to wrap the present net software into an Electron packager and cross a singular machineID inside so as to use its hash as a salt for the important thing derivation.
Thus we may save the acquainted interface and all the pieces you’re used to within the net model. We didn’t need to damage your person expertise so you possibly can nonetheless unlock the app with a brief PIN as an alternative of memorizing sturdy and heavy passwords. In the long term, desktop model provides choices in comparison with the online model.”
[ad_2]
Source link


