[ad_1]

A compromised Trezor {hardware} pockets mailing listing was used to ship pretend information breach notifications to steal cryptocurrency wallets and the property saved inside them.
Trezor is a {hardware} cryptocurrency pockets that means that you can retailer your crypto property offline, relatively than utilizing cloud-based wallets or wallets saved in your PC which are extra susceptible to theft.
When organising a brand new Trezor, a 12 to 24-word restoration seed might be displayed that permits homeowners to get well their wallets if their gadget is stolen or misplaced.
Nonetheless, anybody who is aware of this restoration seed can achieve entry to the pockets and its saved cryptocurrencies, making it important to retailer the restoration seed in a secure place.
Beginning as we speak, Trezor {hardware} pockets homeowners started receiving information breach notifications prompting recipients to obtain a pretend Trezor Suite software program that may steal their restoration seeds.
Trezor confirmed on Twitter that these emails have been a phishing assault despatched by way of one in all their opt-in newsletters hosted at MailChimp.
Trezor later stated that MailChimp allegedly confirmed their service was compromised by an “insider” focusing on cryptocurrency firms.
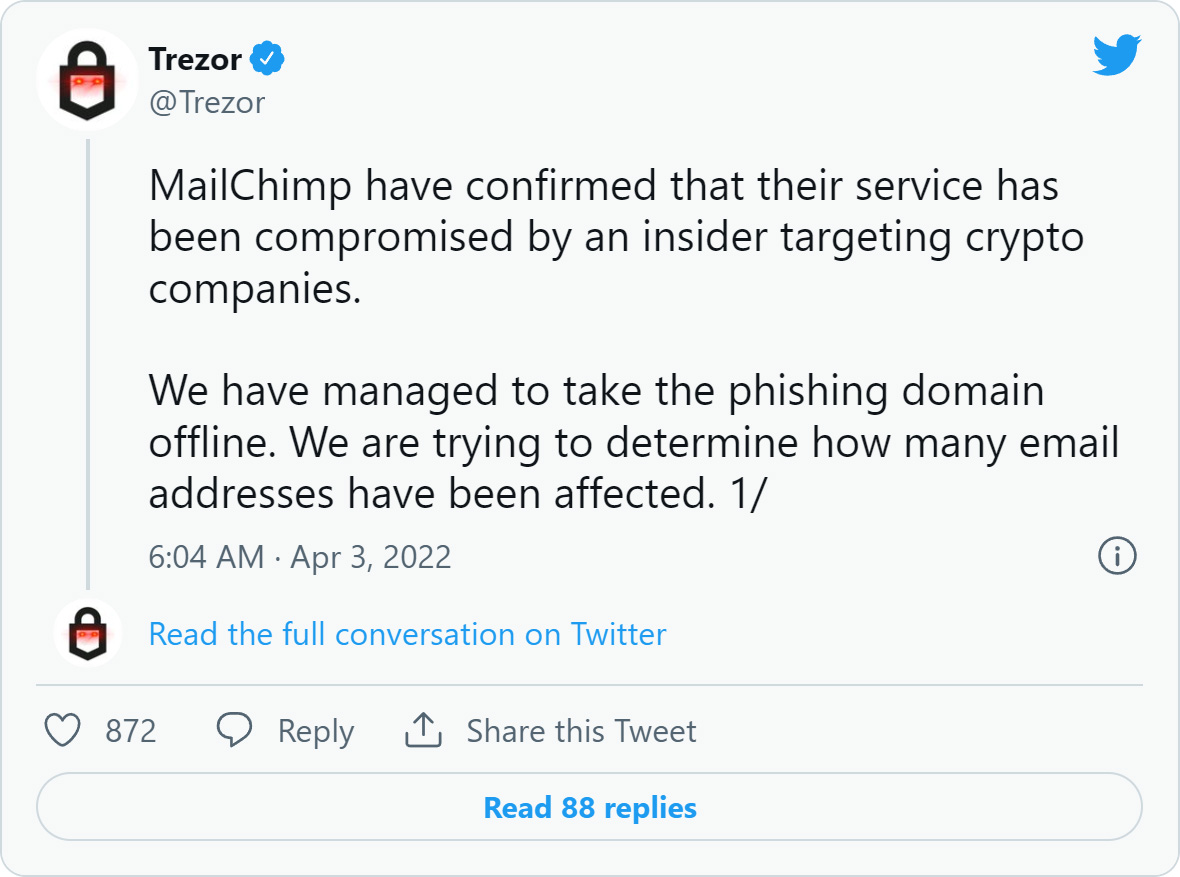
BleepingComputer has contacted MailChimp to study extra about this compromise however has not acquired a reply right now.
A deeper take a look at the Trezor assault
The phishing assault began with the Trezor {hardware} pockets homeowners receiving pretend safety incident emails claiming to be a knowledge breach notification.
“We remorse to tell you that Trezor has skilled a safety incident involving information belonging to 106,856 of our prospects, and that the pockets related along with your e-email handle [email here] is inside these affected by the breach.,” reads pretend Trezor information breach phishing e mail.
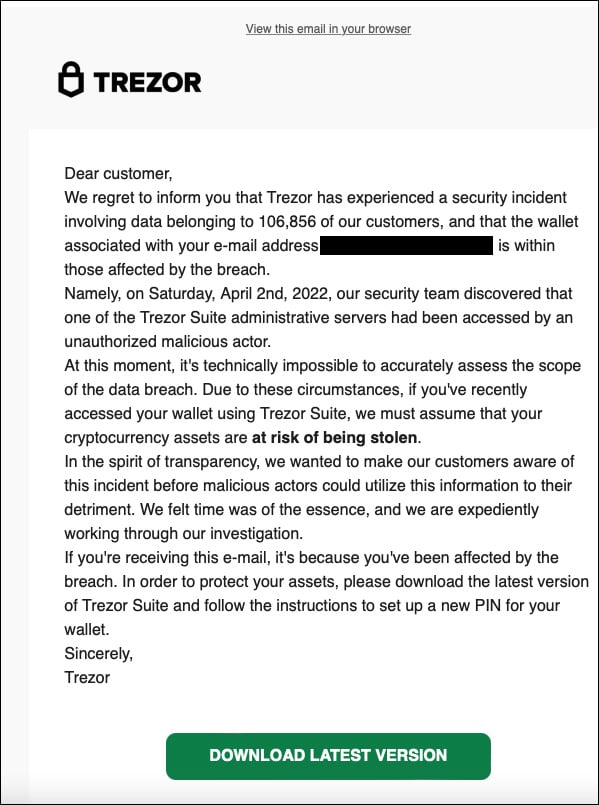
Supply: Twitter
These pretend information breach emails say that the corporate doesn’t know the extent of the breach and that homeowners ought to obtain the most recent Trezor Suite to arrange a brand new PIN on their {hardware} pockets.
The e-mail features a ‘Obtain Newest Model’ button that brings the recipient to a phishing website that seems within the browser as suite.trezor.com.
Nonetheless, the web site is a domain name using Punycode characters that permits the attackers to impersonate the trezor.com area utilizing accented or Cyrillic characters, with the precise area identify being suite.xn--trzor-o51b[.]com.
It ought to be famous that the authentic Trezor web site is trezor.io.
This pretend website prompts customers to obtain the Trezor Suite software, as proven beneath.
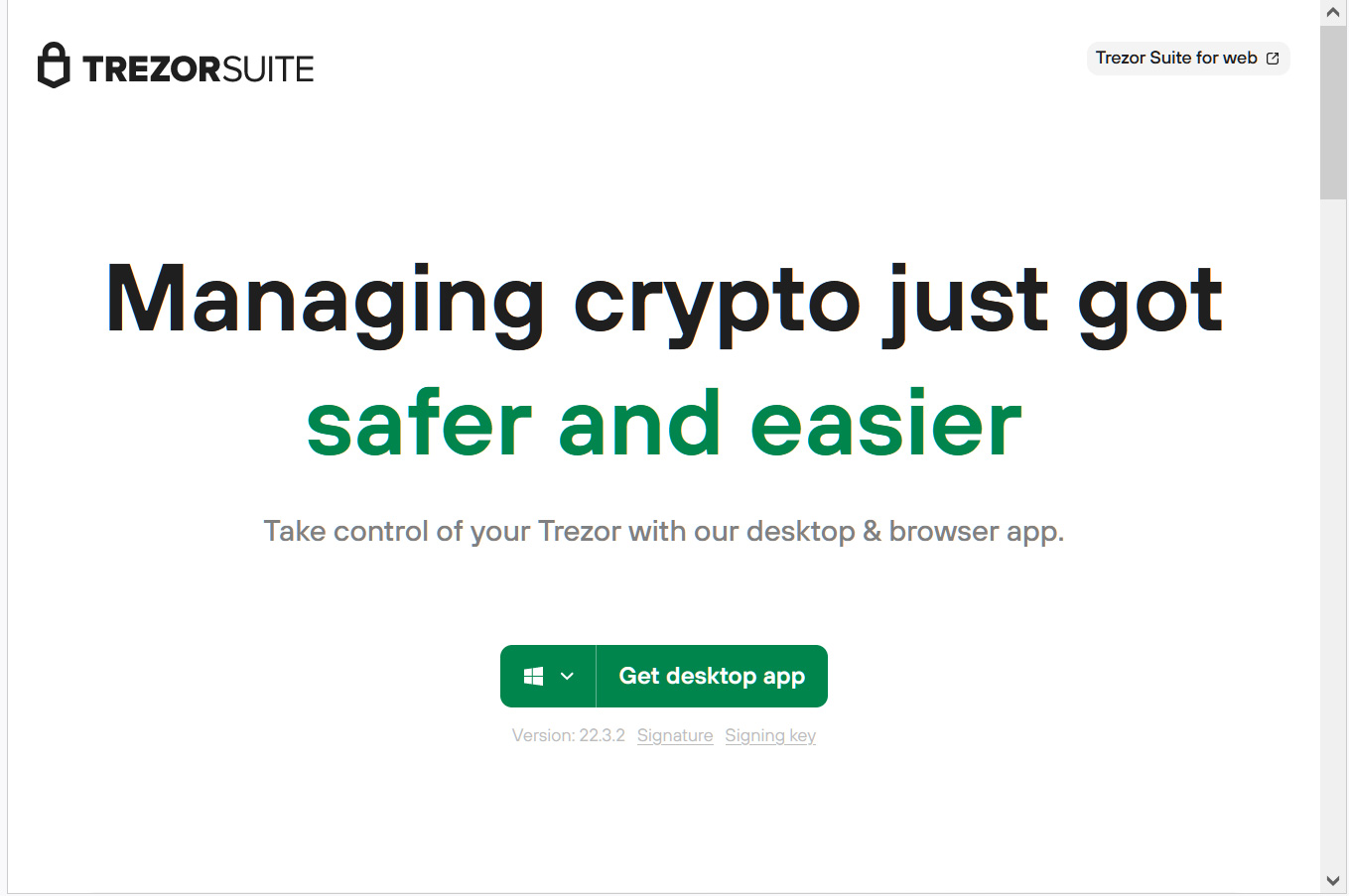
Supply: BleepingComputer
Along with the suite.xn--trzor-o51b[.]com web site, the risk actors additionally created phishing websites on the URLs:
http://trezorwallet[.]org/
trezor[.]us
http://suite.trezoriovpjcahpzkrewelclulmszwbqpzmzgub37gbcjlvluxtruqad[.]onion/ (Tor website)When a customer downloads the desktop app, it would obtain a pretend Trezor Suite software from the phishing website named ‘Trezor-Suite-22.4.0-win-x64.exe’.
As you may see beneath, the authentic Trezor Suite software is signed utilizing a certificates for “Satoshi Labs, s.r.o.” and the pretend Home windows model [VirusTotal] is signed by a certificates from “Neodym Oy” (proper).
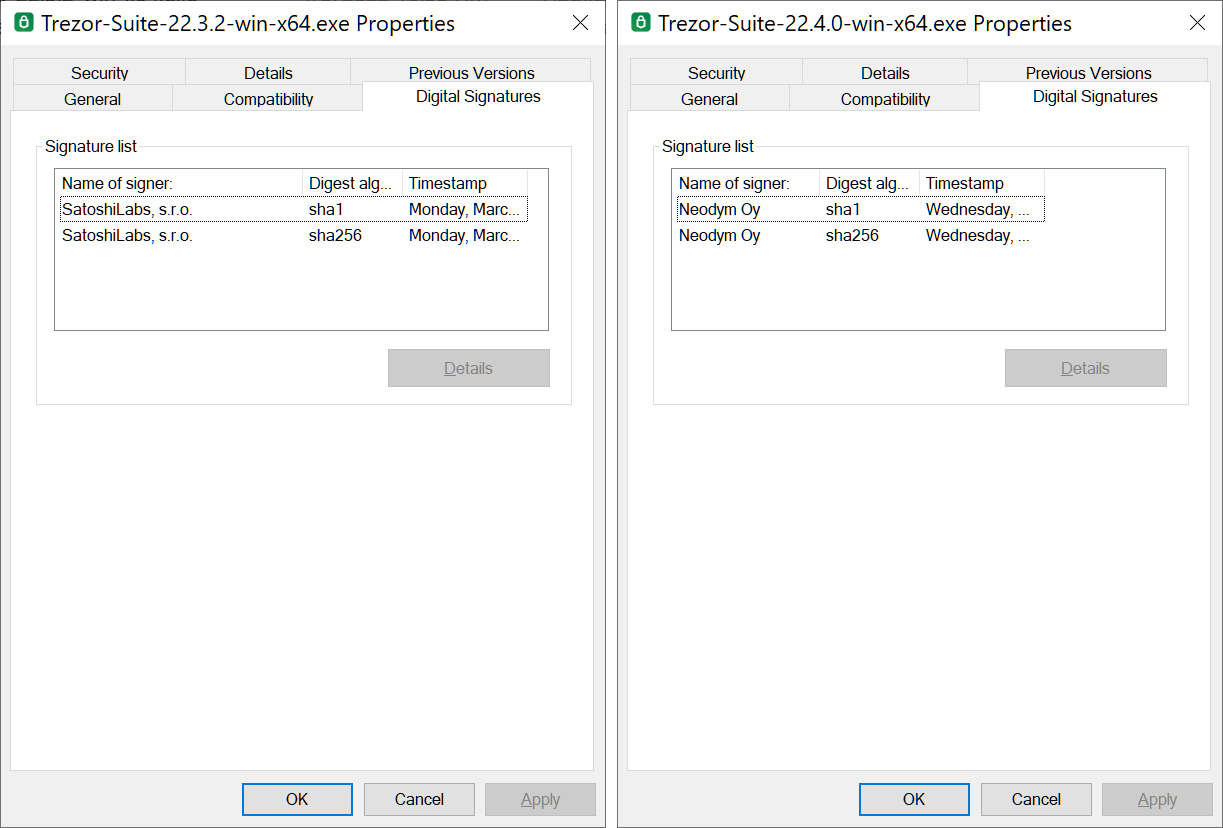
Supply: BleepingComputer
Because the Trezor Suite is open supply, the risk actors downloaded the supply code and created their very own modified app that appears similar to the unique, authentic software.
Sarcastically, this pretend suite even consists of Trezor’s warning banner about phishing assaults on the prime of the appliance’s display screen.
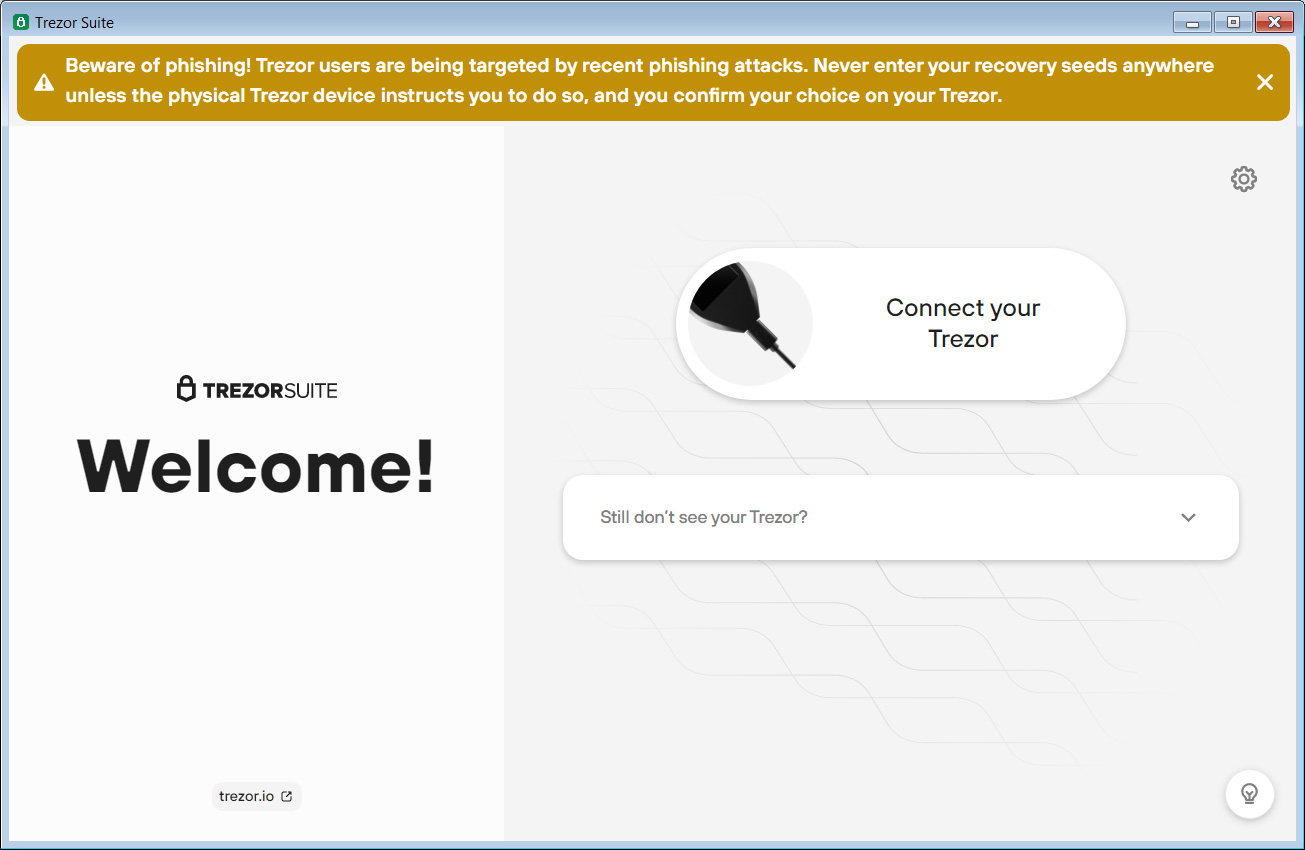
Supply: BleepingComputer
Nonetheless, as soon as Trezor homeowners join their gadget to the pretend Trezor Suite app, it would immediate them to enter their 12 to 24-word restoration phrase, which is distributed again to the risk actors.
Now that the risk actors have your restoration phrase, they’ll use it to import the restoration phrase into their very own wallets and steal victims’ cryptocurrency property.
An almost identical attack focused Ledger {hardware} crypto pockets homeowners want phishing assaults resulting in pretend Ledger Reside software program.
What ought to Trezor homeowners do?
In the beginning, by no means enter your restoration seed in any app or web site. The seed ought to solely be entered instantly on the Trezor gadget you are attempting to get well.
As it’s straightforward to create lookalike domains that impersonate authentic websites, on the subject of cryptocurrency and monetary property, at all times kind the area you are attempting to succeed in into your browser relatively than counting on hyperlinks in emails.
This manner, you already know you will the authentic website relatively than a website impersonating it.
Moreover, Trezor’s official web site is at trezor.io, so different domains, corresponding to trezor.com, are unrelated to the crypto {hardware} pockets firm.
Lastly, disregard any emails claiming to be from Trezor stating that you just have been affected by a latest information breach. In case you are involved, relatively than click on on the hyperlink in these emails, contact Trezor instantly for extra info.
[ad_2]
Source link


